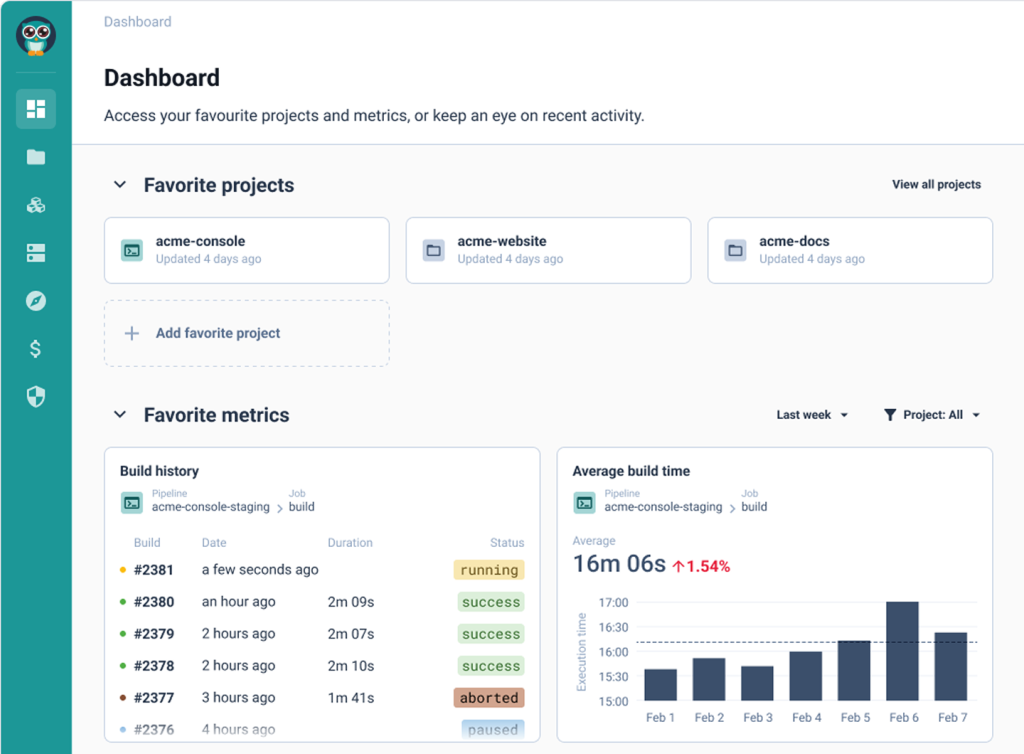
Cycloid vs Port
A Terraform apply runs cleanly through CI; no errors, no warnings, green across the board. Two engineers spin up a proof-of-concept cluster for a performance test, forget to tag it, and leave it running over a long weekend. Three weeks later, a $14,000 line item shows up in the cloud billing dashboard and nobody can immediately tell which team owns it, which workspace created it, or whether any approval was ever required.
When those incidents start repeating, platform teams open a shortlist. Port usually appears on it because the organization can’t tell what infrastructure exists, who owns it, or whether it meets internal standards like required tags, defined on-call ownership, or passing security scans. Cycloid usually appears because infrastructure changes are executed without proper review, policy checks are informal at best, and the only thing standing between a developer and a production apply is a Slack message to the right person.
The procurement spreadsheet drops them in the same row because both have service catalogs and both have self-service workflows. Port organizes knowledge about what exists: which services are running, which team owns them, whether they carry required metadata like on-call contact, deployment frequency, or SLA tier. Cycloid controls what executes: who can run a Terraform plan, whether that change passes policy before it touches a cloud provider, and what it’s estimated to cost before the apply button is available at all. Conflating the two is roughly like comparing a circuit breaker to a wiring diagram. Both matter; neither does what the other does. And buying the wrong one doesn’t fix the original problem, it just gives you something polished to demo while the actual failure keeps recurring.
What follows works through both products at the layer where it counts: execution, governance, state ownership, and what the platform actually controls once compliance enters the picture.
Where Should Platform Control Sit?
Platform teams usually surface this question after a specific incident rather than as a strategic exercise. A Terraform workspace applies a change that nobody reviewed. A proof-of-concept environment stays running for six months because the engineer who created it left and ownership was never recorded. A staging config diverges from production, and nobody finds out until something breaks on the wrong side.
At that point, teams tend to split into two camps. The first camp’s problem is that infrastructure changes are escaping any meaningful review. The second camp’s problem is that nobody can tell what exists, who owns it, or whether it meets internal standards. Both camps may eventually need both tools. But the purchase decisions, the onboarding effort, and the org-level change required are completely different, and conflating the two wastes time.
Cycloid was built for the first camp. It intercepts infrastructure delivery at the execution layer, runs policy and cost checks before terraform apply, and keeps state centrally so drift doesn’t accumulate silently across workspaces.
However, Port was built for the second camp. It centralizes knowledge about software and infrastructure assets into a catalog that updates in real time via integrations, then lets teams build scorecards, dashboards, and self-service workflows on top of that data.
Neither tool replaces the other. The question is which problem you’re paying for right now.
Feature Comparison: Cycloid vs Port
This comparison is written for platform engineers and DevOps leads making a concrete decision. The focus is on where enforcement happens, what the platform actually owns, and what you still have to build or wire together yourself.
1. Deployment, Architecture and Data Boundaries
Cycloid offers three deployment options: shared SaaS, a dedicated managed instance, or fully self-hosted inside a customer’s private network, including environments with no outbound internet access. The reason that flexibility matters is specific: when Cycloid runs a Terraform plan or apply, it handles AWS access keys, GCP service account credentials, Azure service principals, and the state files those runs produce. Approval records, execution logs, and policy evaluation results all live inside the platform’s runtime. For financial institutions, defense contractors, or any organization under data sovereignty regulation, those artifacts can’t touch infrastructure outside a defined perimeter. The self-hosted option puts the entire control plane, credentials, state, and logs, inside the customer’s own network.
Read MoreLess
Port‘s deployment story starts from a different premise. Because Port doesn’t execute infrastructure changes or run Terraform directly, it never holds cloud provider credentials in the first place. What Port ingests is metadata: Kubernetes resource definitions, GitHub repository details, PagerDuty service ownership records, Datadog monitor states, CI/CD pipeline run results. Ocean integrations, Port’s data-syncing layer, can run as agents inside a customer’s network to pull that metadata without exposing internal systems, while the catalog and portal themselves remain on Port’s cloud infrastructure. Enterprise customers can request Private Link connectivity or discuss dedicated tenancy, but the runtime stays SaaS.
The practical boundary here is what each platform touches. A regulated team running Cycloid self-hosted keeps every credential, every state file, and every approval record inside their own perimeter. A team running Port keeps only catalog metadata in Port’s cloud: service names, ownership records, scorecard results, and integration-sourced properties. Neither model is wrong. The question is whether your compliance requirements extend to IaC execution and credential handling, or only to the organizational metadata layer.
Takeaway: Cycloid is the right fit when deployment and hosting requirements extend to IaC execution, credential handling, cost governance, and policy enforcement sitting inside a controlled network. Port fits when the requirement is a SaaS developer portal and internal developer platform that surfaces organizational knowledge without owning the infrastructure execution path.
FEATURE

CYCLOID
PORT
Deployment models
Shared SaaS, dedicated managed instance, or fully self-hosted including air-gapped and fully isolated private networks
SaaS only; enterprise customers can request dedicated tenancy and Private Link connectivity
Data residency control
Full control when self-hosted; state files, execution logs, credentials, and approval records stay entirely within customer-controlled infrastructure
Data stored in customer-dedicated databases on AWS; Ocean agents can run inside the customer’s network, but the portal and catalog runtime remain on Port’s cloud
Platform runtime ownership
Customer or Cycloid manages the full control plane depending on the chosen deployment model
Port operates the AWS-hosted runtime; customers control configuration but have no access to the underlying infrastructure
Infra credentials handling
AWS access keys, GCP service accounts, Azure service principals, and Terraform state files are stored and used within the platform’s runtime during plan and apply
Port does not store customer credentials; all cloud access happens in systems external to Port
Regulated environment fit
Suitable where IaC execution, credential handling, policy enforcement, and state storage must remain inside a private or isolated network
Suitable where compliance requirements apply to catalog metadata and organizational data, but not to IaC execution or cloud credential handling
2. Infrastructure Delivery and State Management
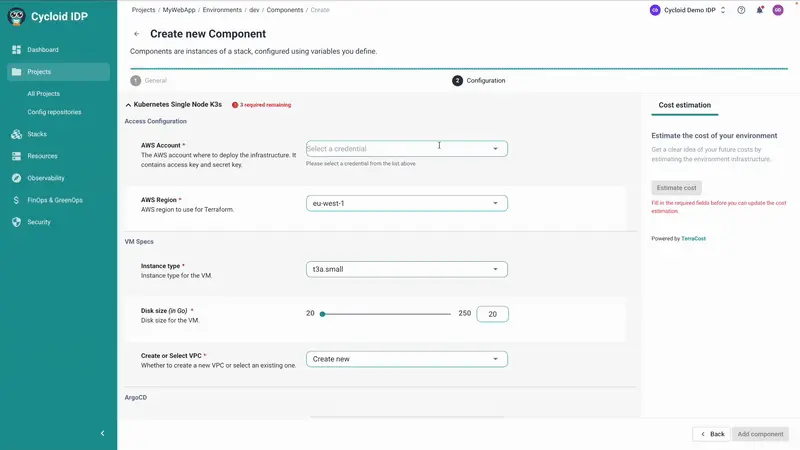
This is where the products stop overlapping entirely. Cycloid executes infrastructure changes. Platform engineers define Stacks, which are Git-backed Terraform or Ansible configurations, and developers request environments or changes against those Stacks through a governed workflow. Cycloid runs the plan, applies it after required approvals, and tracks state centrally across environments. It also detects drift by comparing live infrastructure against declared configuration, per environment, per Stack.
Read MoreLess
Port doesn’t run infrastructure; it ingests data from the tools that do. Using its Ocean integration framework or direct API connections, Port can pull Terraform state data, Kubernetes resource data, AWS/GCP/Azure resource metadata, CI/CD run results, and dozens of other sources into its software catalog. Catalog entries update in real time, and you can build dashboards and scorecards on top of that data. But Port has no concept of a Terraform workspace it owns, no mechanism to trigger a plan, and no mechanism to block an apply. Those responsibilities live in whatever CI/CD or IaC tooling already exists.
If a production environment drifts from its declared state, Cycloid surfaces that drift automatically because it owns the state. In Port, you’d know about it only if your external Terraform tooling reports state data to the catalog, and only if you’ve built a scorecard or alert to surface deviations from it.
Takeaway: Cycloid owns the delivery path and uses that ownership to detect drift, enforce policy, and track every state transition. Port ingests data from the tools that do those things and makes it queryable, but it doesn’t own any of it.
FEATURE

CYCLOID
PORT
IaC execution
Runs Terraform and Ansible plans and applies natively as part of the delivery workflow
Does not execute IaC; surfaces data from external IaC tools via integrations
Terraform state management
Centrally tracks state across environments and workspaces
Can ingest state data via integrations but does not own or manage state
Drift detection
Compares declared configuration against live infrastructure per environment
No native drift detection; depends on external tooling reporting state data to the catalog
Environment lifecycle
Creates, updates, and decommissions environments through controlled platform workflows
Environment lifecycle handled entirely in external CI/CD and IaC systems
Infrastructure topology
InfraView shows live topology tied to each environment and Stack
Catalog shows resource metadata and relationships based on ingested data
3. Self-Service and the Developer Interaction Model
Both platforms offer self-service, but the underlying model differs significantly.
Cycloid‘s self-service runs through StackForms: configurable input forms that present developers with a constrained set of options, region, instance type, environment tier, and so on, all bounded by what the platform team has allowed. A developer filling out a StackForm isn’t writing Terraform or modifying a module; they’re selecting from pre-approved values that feed into a Git-backed Stack. The platform validates inputs, runs any required policy checks, triggers the approval workflow, and executes the change. Governance isn’t something a developer can opt out of by choosing a different input.
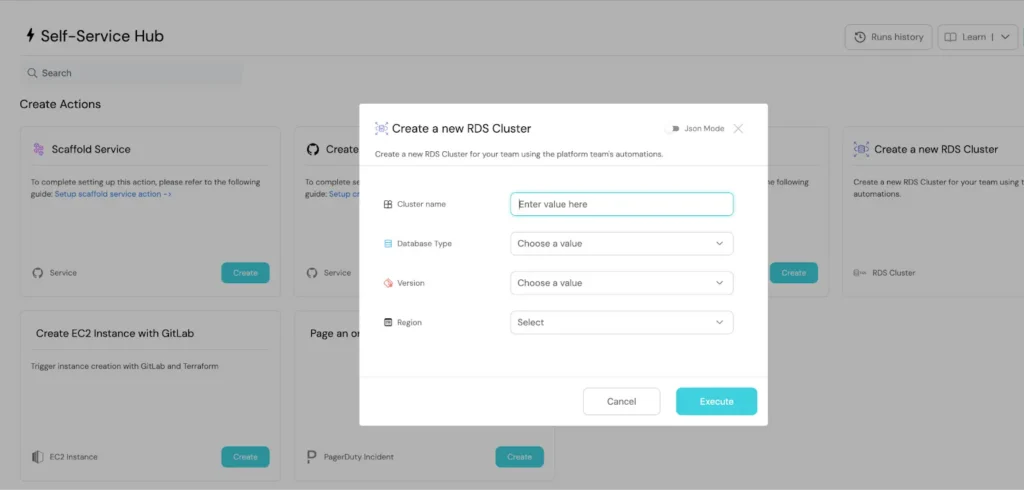
Port‘s self-service is designed differently i.e., platform engineers define self-service actions tied to blueprints, the core modeling unit in Port. An action can trigger a webhook, a GitHub Actions workflow, a Jenkins pipeline, or any external automation. Port handles the form input, the optional manual approval, and the audit event. The actual work happens outside Port, in whatever CI or IaC system the action points to. This means Port’s self-service is as strong as the external system it’s calling. If that system lacks its own guardrails, Port doesn’t add them.
Read MoreLess
Cycloid’s tighter coupling gives you more control over what executes. Port’s loose coupling gives you more flexibility to plug into an existing toolchain without displacing it.
Takeaway: Cycloid reduces ticket load by standardizing how infrastructure is requested and what it can produce. Port reduces cognitive load by centralizing where actions live, while leaving execution to systems the platform team already manages
FEATURE

CYCLOID
PORT
Self-service mechanism
StackForms with bounded inputs feeding Git-backed Stacks; governance baked into the workflow
Action forms triggering external automations via webhooks, GitHub Actions, Jenkins, etc.
Guardrails on inputs
Input options predefined by platform team; invalid combinations blocked before execution
Input validation at the form level; enforcement depends on what the external automation implements
Approval flow
Built-in approval steps before plan and apply run
Manual approval toggles configurable per action; approval notification via email, Slack webhook, or API
What happens if policy fails
Change is blocked before apply
Depends on what the triggered external system does when it receives the payload
Execution coupling
Tightly coupled; platform owns the execution path
Loosely coupled; platform delegates execution to external tools
4. Access Control, Governance, and Auditability
Both platforms have RBAC, and both have audit logs, but they govern different things.
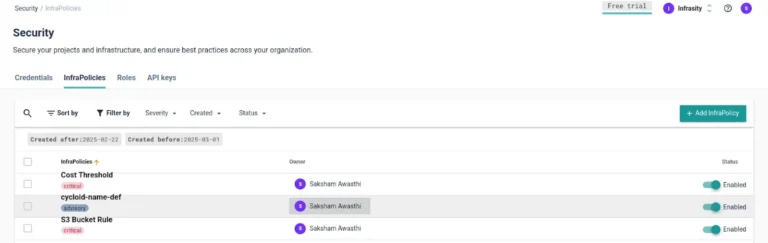
Cycloid‘s access control operates at the Stack and environment level. A role definition controls whether a user can request an environment, approve a plan, run a plan without approval, or trigger an apply. Policy as Code (using OPA) runs before Terraform executes, evaluating inputs, target environments, and resource types before anything reaches the cloud. When a change is blocked, it’s blocked at the platform level regardless of whether the underlying Git repository would have allowed it or whether the CI pipeline was configured loosely.
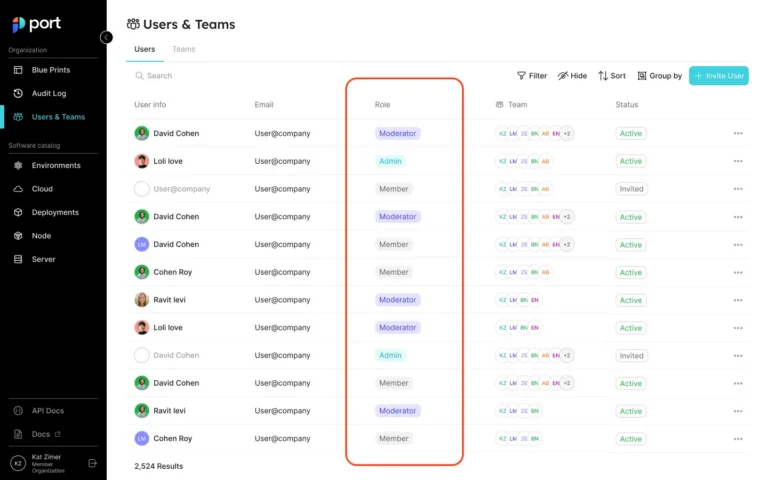
Port‘s RBAC controls who can view, create, or modify catalog entities and who can invoke self-service actions. Permissions can be set by role (admin, moderator, member), by team membership, or by dynamic rules using JQ expressions against catalog data. For example, you can write a policy that allows only the on-call engineer to trigger a rollback action on a given service. Port also maintains an audit log that records every catalog modification, action invocation, and automated event, including which user or service account triggered it.
Read MoreLess
The distinction is about where enforcement actually bites. Port’s RBAC stops unauthorized users from invoking actions through Port. It doesn’t stop those same users from triggering the same pipeline directly from their CI system, pushing to the Git repository, or running Terraform from their laptop. Cycloid’s enforcement runs in the delivery path itself, so bypassing it requires bypassing the platform.
Takeaway: Cycloid enforces governance before changes reach production. Port describes compliance through scorecards and ownership that must already be enforced in the systems Port integrates with.
FEATURE

CYCLOID
PORT
RBAC scope
Stack and environment level; roles control who can request, approve, plan, or apply infrastructure changes. Permissions are enforced at execution, not just at the portal layer
Catalog and action level; admin, moderator, and member roles control who can view or edit entities and invoke actions. Dynamic permissions via JQ expressions allow context-aware access, for example, restricting production deployments to senior engineers only
Policy enforcement
OPA-backed InfraPolicies evaluate inputs, target environment, and resource type before Terraform plan and apply run. Non-compliant changes are blocked at the platform level regardless of what the underlying Git repository or CI pipeline permits
Port automations use JQ-based condition rules to enforce policies on action runs: blocking deployments with critical vulnerabilities detected by scanners like Trivy or Wiz, auto-approving low-risk requests, and escalating high-risk ones. This policy logic runs inside Port but acts on Port-managed action runs, not directly on Terraform or IaC execution
Approval workflows
Native approval steps are configured per Stack and environment. A plan does not proceed until required approvers act. Approver roles are defined in Cycloid’s RBAC model
Per-action requiredApproval field set to ANY (any one approver sufficient) or ALL (every designated approver must act). When an action is triggered, it enters WAITING_FOR_APPROVAL status and sends an email notification to approvers. Approvers act from the Port UI or via API. Slack notifications require a separate automation
Audit logging
Centralized logs capture the request, approver identity, policy evaluation result, and the infrastructure change produced, all in one record tied to the Stack and environment
Port maintains an audit log of every catalog change, action invocation, approval decision, and automation trigger, including the user or service account that initiated each event. Execution logs from the downstream CI/CD or IaC system remain outside Port
Compliance posture
Non-compliant infrastructure changes are blocked before they execute, because Cycloid owns the execution path. A policy failure stops the plan regardless of what any upstream system would have permitted
Compliance is tracked through scorecards measuring criteria like branch protection, IAM hygiene, dependency management, and encryption standards. Policies run on Port-managed action runs. Compliance enforcement on raw IaC execution requires the downstream CI/CD system to carry it
5. Cost Visibility and FinOps Controls
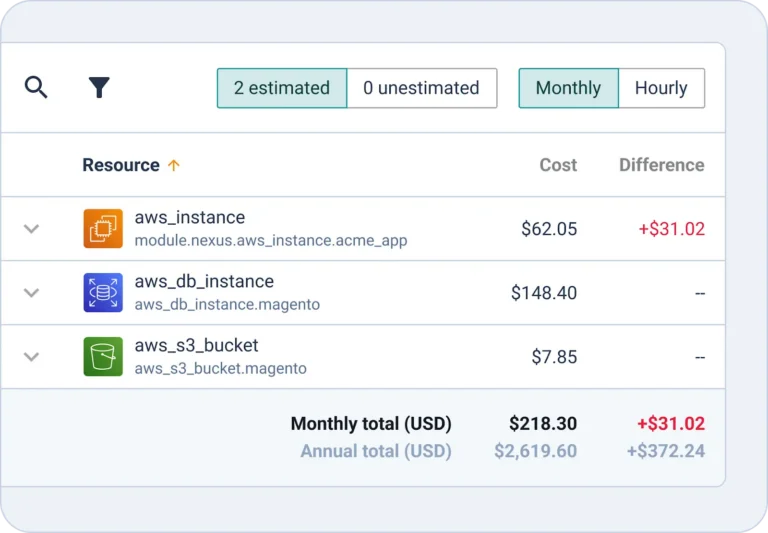
Cycloid runs cost estimation as part of the Terraform plan. Before an apply proceeds, the platform calculates expected cloud spend for the change and can block it if budget thresholds defined in policy are exceeded. This puts the cost check in the same gate as the policy check and the approval. Carbon footprint tracking runs alongside cost data, both visible in a FinOps module that aggregates spend by environment, Stack, and project across cloud providers.
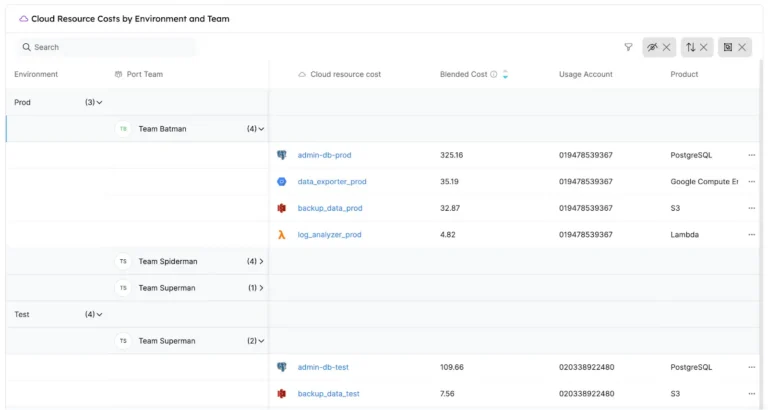
Port‘s approach to cost is catalog-based. When you connect a cost data source (via integrations), cost information flows into the software catalog and gets attached to the entities that own the resources. You can then build dashboards showing spend by team, service, or domain, which is genuinely useful for driving cost accountability conversations. What Port doesn’t do is act on that data. It doesn’t gate a deployment, block a change, or reject a self-service action based on estimated cost. Cost insight in Port is post-hoc; cost control in Cycloid runs pre-apply.
Read MoreLess
Takeaway: Cycloid shifts cost and sustainability checks into the delivery gate, blocking over-provisioned infrastructure before it exists. Port gives teams visibility into what was already spent and which team owns it.
FEATURE

CYCLOID
PORT
Pre-deploy cost estimation
Calculates estimated cost as part of the Terraform plan before apply runs
Does not evaluate cost during infrastructure changes
Budget enforcement
Budget thresholds configurable as policy checks that block plans or applies
No mechanism to block deployments based on cost
Cost visibility
Real-time cloud spend aggregated by environment, Stack, and project across providers
Cost data surfaced via integrations in the catalog, mapped to services, teams, and domains
Carbon footprint tracking
Carbon footprint tracked per deployed infrastructure alongside FinOps data
Not collected or evaluated natively
Cost control timing
Evaluated before resources are created or modified
Visible only for resources that already exist
6. Data Model and Catalog Flexibility
Port’s core differentiator relative to simpler service catalogs is its Blueprint system. A Blueprint is a custom entity type: you can model anything, a microservice, an environment, a Kubernetes cluster, a database, a team, a cost center, and define properties, relationships, and mirror properties that reflect data from related entities. That flexibility means Port’s catalog can represent the actual structure of your organization rather than forcing you into a fixed taxonomy.
Cycloid’s service catalog is organized around Stacks. A Stack is a Git-backed infrastructure template: it defines the Terraform or Ansible configuration, the input schema, and the environment-level constraints. The catalog gives teams a curated list of approved infrastructure configurations rather than a general-purpose graph of all organizational entities. This scope difference is intentional: Cycloid’s catalog is the entry point to governed infrastructure delivery, not a general metadata store.
Organizations that need to catalog and relate dozens of asset types across engineering, security, SRE, and product domains will find Port’s flexibility valuable. Organizations that want to standardize and govern infrastructure delivery will find Cycloid’s Stack-based catalog does exactly what’s needed, without requiring a data modeling exercise before anyone can deploy anything.
Cycloid or Port:
How to Choose the Right Platform for Your Engineering Team
Platform teams pick the right tool for the wrong problem, deploy it, present it at a team meeting, and then wonder six months later why the original incidents are still happening.
If your recurring incidents trace back to infrastructure delivery, unreviewed plans, environments that differ between stages in ways nobody can explain, or changes that slipped past policy because approval happened in a Slack thread, the problem is in the execution path. The cycloid sits in that path by design. It doesn’t describe what should happen; it enforces what does.
If your recurring friction is organizational, developers don’t know which service owns a dependency, onboarding takes weeks because nobody can find the right repository, cost reports can’t be attributed to a team because the tagging model doesn’t match the org chart, the problem is knowledge and coordination. Port addresses that by giving platform engineers a flexible data model to represent what actually exists and connect it to the people responsible for it.
Want to see how Cycloid can help you achieve your goals?
If the information above is inaccurate or outdated, please contact us at marketing@cycloid.io and we’ll set it right straight away!