Cycloid vs Compass
What starts as well-structured Terraform repositories and protected branches often fragments. Teams fork modules to move faster, environment variables drift between workspaces, and IAM roles expand because narrowly scoped permissions break pipelines or block routine deployments under deadline pressure. Approvals move from enforced policy to Slack messages. Platform engineers spend time reviewing plans and tracing state files instead of improving the system.
Teams compare Cycloid and Compass when specific failure patterns repeat. A service breaks and no one knows which team owns the deploy pipeline. A Terraform change applies successfully, but later turns out to have bypassed required plan checks or environment restrictions. A deployment passes CI, yet violates internal standards that were never enforced anywhere.
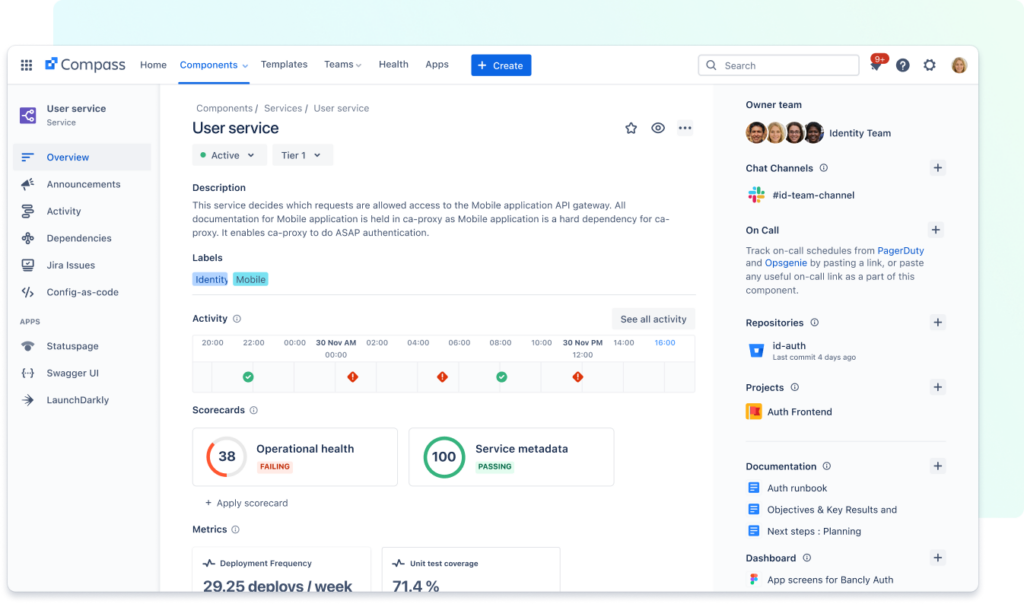
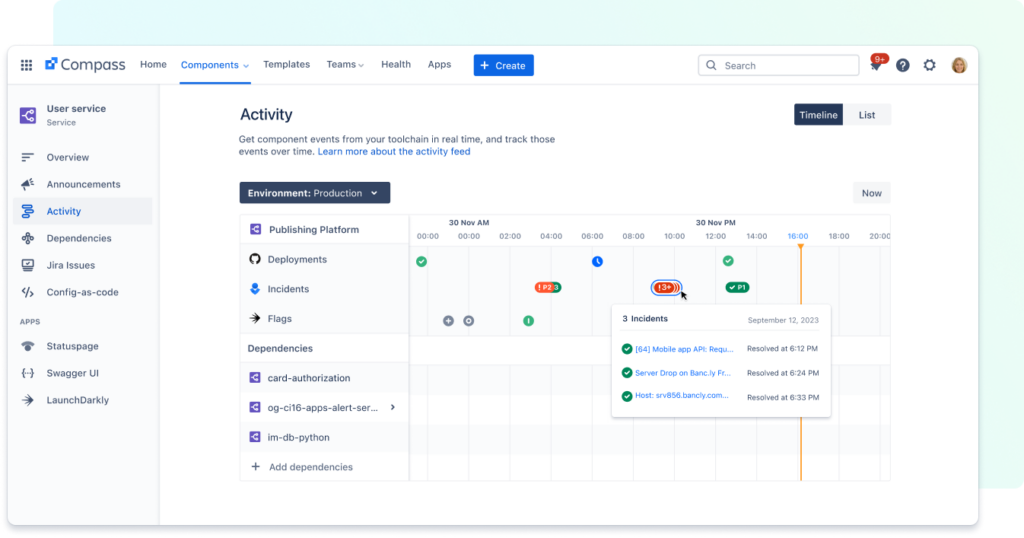
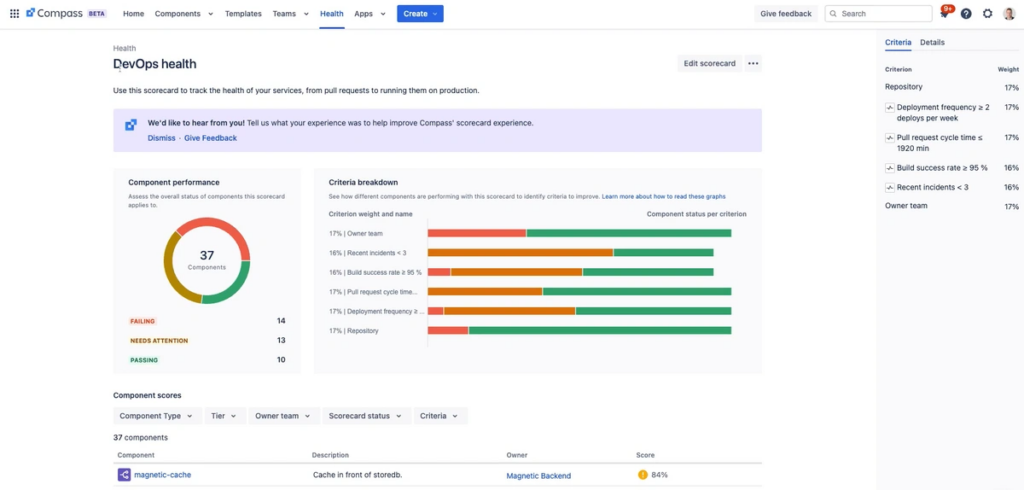
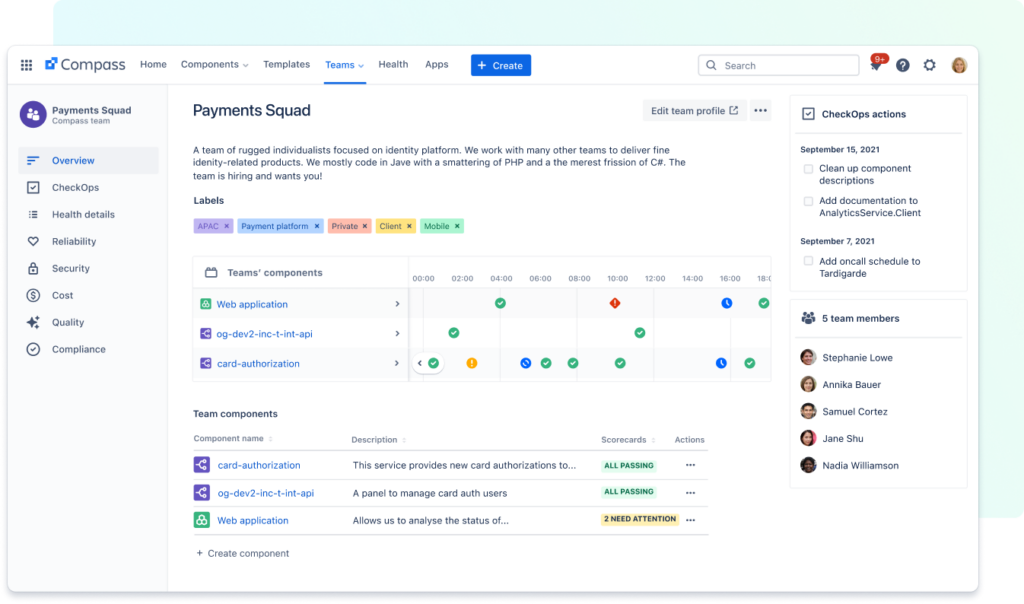
Compass addresses the visibility gap around services i.e., it helps teams identify which service owns a deployment pipeline, where its source repository lives, which CI jobs publish it, and whether expected signals like test status, on-call ownership, or deployment frequency are present. It surfaces context, but it does not control how changes are executed. Cycloid addresses the execution gap i.e., it controls who can run Terraform plans and applies, which variables can be modified per environment, and whether policy and cost evaluations run before infrastructure reaches the cloud. Instead of describing standards, it enforces them in the delivery path. Both improve clarity, but at different layers of the stack. One organizes services and accountability and the other governs how infrastructure changes are executed.
Where Should Platform Control Sit in an Enterprise Stack?
Platform teams usually reach this question after something breaks. For example, A Terraform plan modifies more than expected, a production environment differs from staging in ways no one can explain, or a cost spike traces back to a change that technically passed review but was never evaluated for impact. At scale, these are not rare events, they are recurring operational patterns.
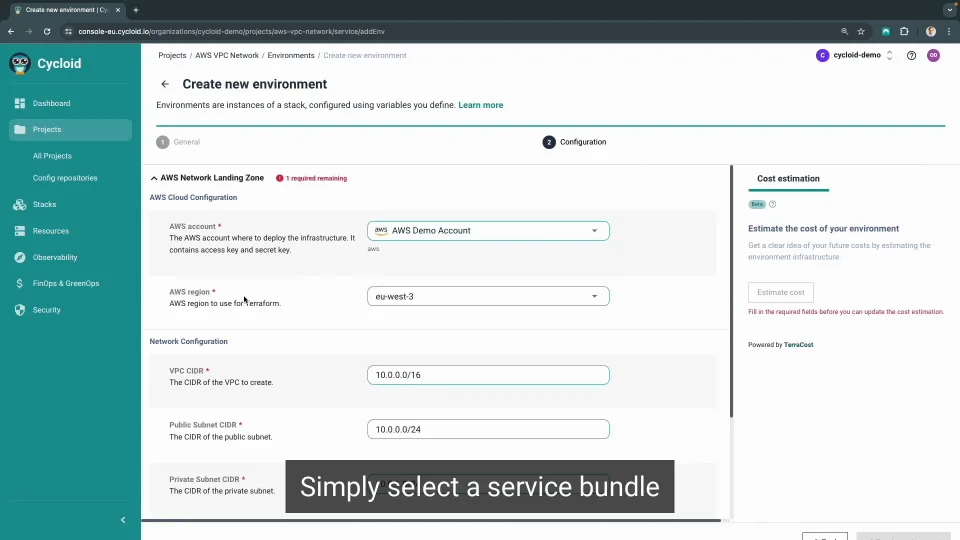
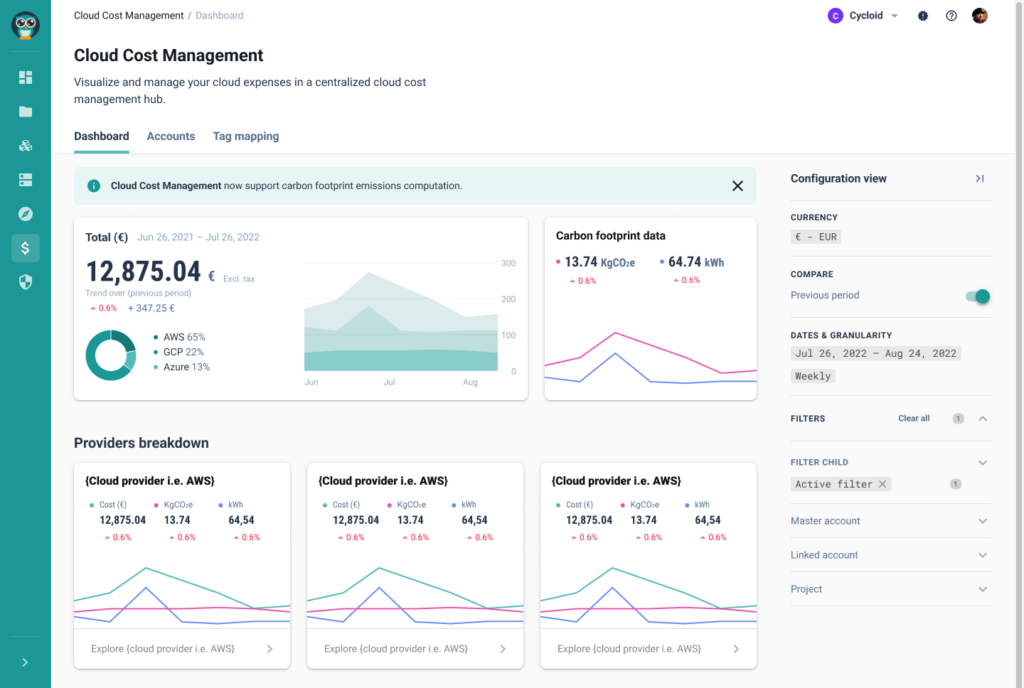
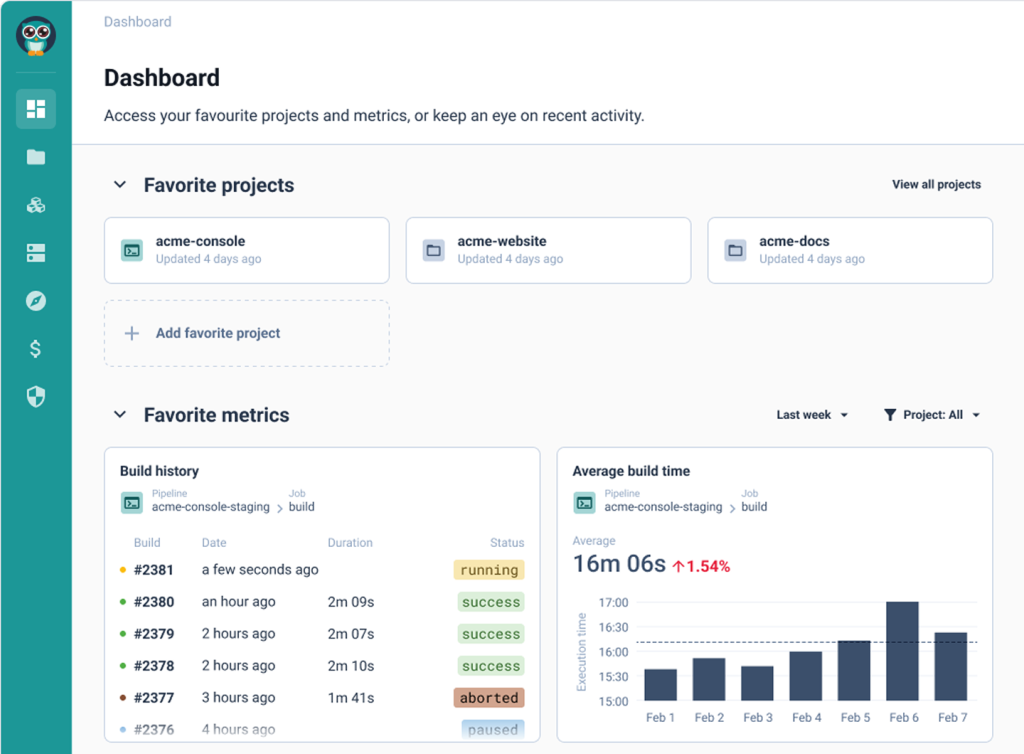
Cycloid is built for teams that treat infrastructure delivery as a production system in its own right. Terraform plans, approvals, policy checks, and cost evaluations run through a defined control path owned by the platform team. Developers still request environments and changes, but execution follows a governed workflow that evaluates scope, permissions, and impact before anything reaches the cloud.
However on the other hand, Compass is built for organizations that already have delivery pipelines in place but struggle to understand what exists. It acts as a service catalog and health layer, mapping services to owners, dependencies, scorecards, and operational signals. Compass stays intentionally outside the execution path.
This difference matters in practice; one platform intercepts infrastructure changes before terraform apply runs by enforcing policy, approvals, and cost checks. The other surfaces information after deployment, showing which services, pipelines, and resources are running, without influencing how those changes were executed.
By the end of this breakdown, you should be able to decide whether your platform problem is lack of control or lack of visibility.
Feature Comparison: Cycloid vs Compass
This comparison is for enterprise platform engineers and DevOps leads who have learned that dashboards alone do not prevent incidents. The focus here is on where enforcement happens, how delivery workflows are structured, and what the platform actually owns once scale and compliance enter the picture.
1. Setup, Maintenance & Hosting Flexibility
The deployment model shapes everything that follows. It affects credential handling, audit scope, and whether the platform itself can be treated as compliant infrastructure.
Cycloid supports SaaS, private managed instances, and fully self-hosted or air-gapped deployments. This is required because Cycloid runs Terraform, policy checks, and cost analysis as part of its control plane. Regulated enterprises often need that control to keep state, credentials, and approvals within defined boundaries.
Read MoreLess
Compass is delivered as a SaaS product inside Atlassian Cloud. It does not manage infrastructure state or credentials, which simplifies its operational footprint. Organizations already standardized on Jira and Bitbucket usually accept this trade-off because Compass sits alongside collaboration tooling rather than infrastructure systems.
This category evaluates how each platform fits into enterprise security and compliance models.
Takeaway: Cycloid fits teams that need infrastructure control planes deployed under strict security or residency requirements. Compass fits teams comfortable with SaaS tooling that augments visibility without touching sensitive execution paths.
FEATURE
CYCLOID
ATLASSIAN COMPASS
Deployment models
Can be run as a shared SaaS, a dedicated managed instance, or fully self-hosted inside the customer’s network, including environments with no outbound internet access
Runs only as part of Atlassian Cloud, requires outbound connectivity to Atlassian services
Data residency control
Infrastructure state, execution logs, and configuration can be kept entirely within customer-controlled regions and networks
Data storage and processing are constrained to Atlassian Cloud regions and policies
Platform runtime ownership
Platform team can operate and upgrade the full control plane or delegate that responsibility to Cycloid under a managed model
Atlassian operates the runtime, customers cannot control upgrade timing or internal behavior
Infra credentials handling
Cloud credentials and Terraform state are stored and used within the platform’s controlled runtime during plan and apply
Does not store or use cloud credentials, all infrastructure access happens in external systems
Regulated environment fit
Suitable where infra state, execution, and approvals must remain inside private or isolated networks
Suitable only where SaaS control planes are permitted and infra execution happens externally
2. Infrastructure Delivery and Resource Control
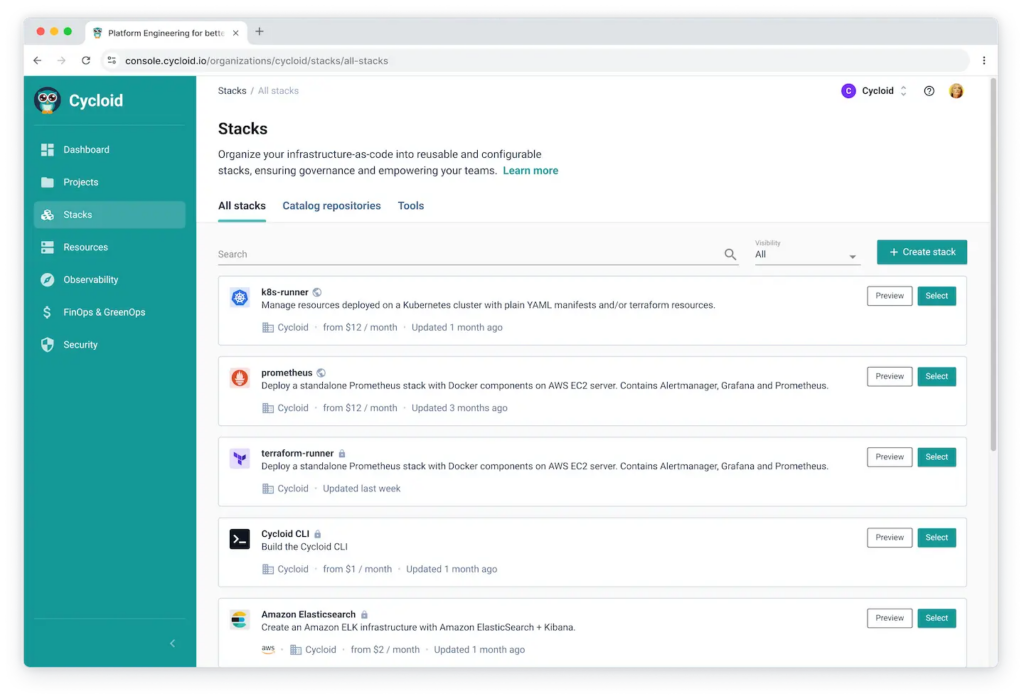
This is where the two platforms diverge most clearly. Cycloid treats infrastructure delivery as a first-class responsibility. Terraform and Ansible runs are executed through Git-backed stacks controlled by the platform. State is tracked centrally, drift is detected automatically, and environment changes follow a consistent path regardless of who initiates them.
Read MoreLess
If your incidents involve unreviewed plans, forgotten proof-of-concept clusters, or production changes from the wrong branch, Cycloid addresses those failure modes directly. Compass does not aim to.
Takeaway: Cycloid exists to prevent infrastructure drift and uncontrolled change by owning execution and state. Compass assumes infrastructure correctness is handled elsewhere and limits itself to describing what exists.
FEATURE
CYCLOID
COMPASS
Infrastructure-as-Code execution
Runs Terraform and Ansible plans and applies as part of the platform workflow
Does not run IaC, execution happens in external CI pipelines
Terraform state awareness
Tracks Terraform state centrally across environments and workspaces
Can link to repositories or tools but does not read or manage state
Drift detection
Compares declared configuration against live infrastructure per environment
No mechanism to detect drift between code and deployed resources
Environment lifecycle control
Creates, updates, and decommissions environments through governed workflows
Environment creation and teardown are handled outside the platform
Infrastructure visualization
Shows live infrastructure topology and resources tied to each environment
Displays service metadata and links without infrastructure topology
3. Self-Service & Developer Interaction
Self-service only works when it reduces friction without increasing risk. Cycloid exposes self-service through controlled inputs mapped to Git-backed infrastructure definitions. Developers request environments or changes, but the platform restricts what can be changed and enforces policy before applying. Every request follows the same approval and execution path.
Read MoreLess
Takeaway: Cycloid reduces ticket load by standardizing how infrastructure is requested and applied. Compass reduces cognitive load by helping developers find the right service, owner, or pipeline without changing how work is executed.
FEATURE
CYCLOID
COMPASS
What a developer can do directly in the platform
Submit a request to create or modify an environment based on approved Terraform stacks
Register, browse, and update service metadata, links, and ownership
How environment creation happens
Platform generates or updates Git-backed stack configuration and triggers controlled Terraform execution
Environment creation must happen in external CI pipelines or Terraform repositories
Guardrails on inputs
Input fields restricted to predefined variables, instance types, regions, and policy-validated parameters
No enforcement on infrastructure parameters, governance handled in external systems
Approval flow
Built-in approval steps before Terraform plan and apply
No native infra approval flow, relies on repository or pipeline-level approvals
What happens if policy fails
Change is blocked before apply
Policy enforcement must exist in external CI or IaC tooling
4. Access Control, Governance, and Auditability
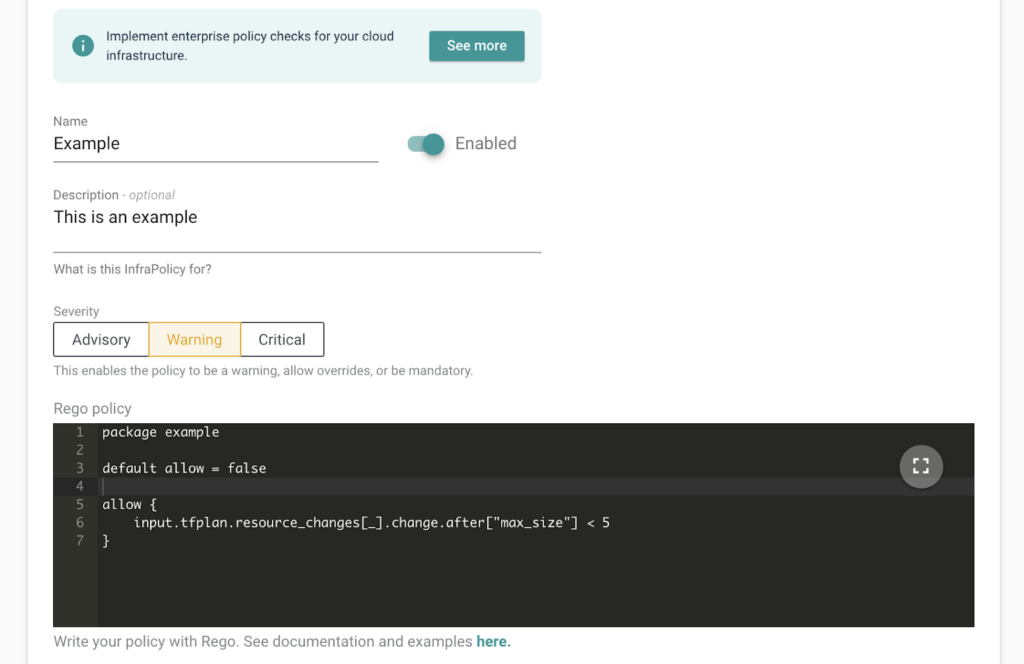
Governance breaks down when it relies on shared understanding rather than enforcement. Cycloid enforces role-based access control and policy checks directly in the delivery workflow. Policies evaluate inputs, environments, and change scope before infrastructure is applied. Audit logs capture requests, approvals, and execution details in one place.
Compass reflects governance rather than enforcing it. If a Bitbucket or GitHub repository allows direct merges to main, or if a CI pipeline is configured to auto-apply Terraform on merge, Compass does not intercept that behavior. Access control for production deployments, Terraform state backends, or cloud IAM roles remains defined in the repository, CI system, or cloud provider.
Read MoreLess
Compass can display who owns a service, whether required checks passed, or whether a scorecard rule is green or red. It cannot stop a pipeline from running terraform apply with elevated permissions, nor can it block a deployment triggered from an unprotected branch. Enforcement lives entirely in the underlying CI, Infrastructure as Code configuration, and cloud identity model.
Takeaway: Cycloid enforces governance before changes reach production. Compass documents governance by reflecting ownership and standards that must already be enforced in downstream systems.
FEATURE
CYCLOID
COMPASS
Role-based access control
Rules are enforced at the stack and environment level, controlling who can request, approve, plan, or apply infrastructure changes
Access is limited to who can view or edit component metadata, permissions are inherited from Atlassian projects and linked repositories
Policy enforcement
Open Policy Agent rules run before Terraform plan and apply, blocking changes based on inputs, target environments, or resource type
No policy evaluation on deployments or infrastructure changes, Compass does not intercept CI or IaC execution
Approval workflows
Native approval steps are part of the delivery workflow, approvals are required before plans or applies proceed
Approvals occur in external systems such as Git pull requests or CI tools, Compass only links to them
Audit logging
Centralized logs capture who requested a change, who approved it, which policy checks ran, and what infrastructure was modified
Audit data is split across Jira issues, Git commits, and CI logs, Compass surfaces references but does not consolidate execution history
Compliance posture
Prevents non-compliant changes from executing by enforcing controls in the delivery path
Describe Compliance status through scorecards and ownership metadata without blocking execution
5. Cost Visibility and Sustainability
Cost overruns usually happen before anyone notices them. Cycloid evaluates cost and sustainability signals as part of infrastructure changes. Teams see estimated impact before applying, and budget thresholds can block changes automatically. This shifts cost control earlier in the delivery cycle.
Read MoreLess
Takeaway: Cycloid shifts cost and sustainability checks earlier, blocking inefficient infrastructure before it is created. Compass improves awareness of spend and accountability but does not influence whether changes proceed.
FEATURE
CYCLOID
COMPASS
Pre-deploy cost estimation
Calculates estimated cloud cost as part of the Terraform plan before apply
Does not evaluate cost during infrastructure changes
Budget enforcement
Applies budget thresholds through policy checks that can block plans or applies
No mechanism to enforce budgets during deployment
Live cost visibility
Aggregates real-time cloud spend by environment, stack, and project
Surfaces cost data only if provided by external integrations
Sustainability signals
Tracks carbon footprint associated with deployed infrastructure
Does not collect or evaluate sustainability data
Cost control timing
Evaluates cost impact before resources are created or modified
Cost visibility is available only after resources already exist
Final Thoughts on the Comparison
Platform teams struggle to understand what is running across dozens of services and environments. Some spend their time responding to tickets for routine changes. In regulated or cost-sensitive environments, risk often appears during experiments, such as a proof of concept where an oversized Dataproc or Hadoop cluster is spun up and left running without visibility, ownership, or budget limits.
This comparison is meant to clarify what each platform takes responsibility for in these situations. It highlights where control is enforced, where workflows are coordinated, and where visibility stops. These boundaries help teams choose a platform that fits how they operate day to day, not just how the architecture looks on paper.
Conclusion – Choosing the Right Platform
Enterprise platform teams rarely fail everywhere at once, failure usually appears at a specific boundary. Either infrastructure changes start escaping review and control, or the organization loses a shared understanding of what services exist, who owns them, and how they are supposed to behave.
Cycloid is built for environments where the cost of uncontrolled delivery is already visible. Terraform plans drift, approvals become informal, and production changes rely on trust rather than enforcement. In those conditions, the platform must own execution, apply policy before changes land, and surface cost and compliance signals early enough to matter.
Compass is built for environments where delivery already works but coordination does not. Services multiply, ownership becomes unclear, and developers spend time tracing dependencies instead of shipping code. Compass restores clarity by centralizing service metadata, health signals, and standards, without stepping into the execution path.
The decision comes down to where your platform team needs leverage today. If your risk shows up during infrastructure change, control has to move closer to delivery. If your risk shows up as confusion, slow onboarding, or unclear accountability, visibility is the missing layer.
Want to see how Cycloid can help you achieve your goals?
If the information above is inaccurate or outdated, please contact us at marketing@cycloid.io and we’ll set it right straight away!